The only
security company
that adds
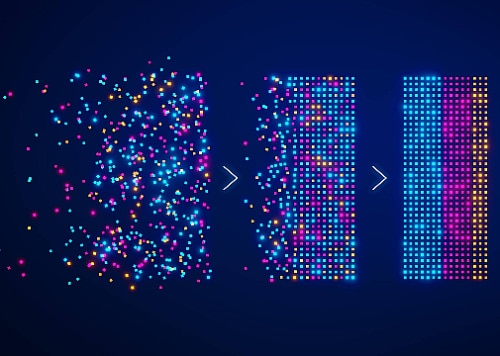
clarity now
Full-range cybersecurity.
BlackLake Security stands out from other solution providers by prioritizing wisdom, transparency, and insight. We focus on understanding each client’s unique culture, issues, and desired outcomes to deliver a comprehensive solution tailored to their circumstances.
Consulting Services
At BlackLake Security, we understand that cybersecurity operation teams must balance security needs with business requirements and new technologies. Our consulting services help clients integrate and implement security solutions while managing compliance and regulatory issues.
Managed Services
BlackLake Security offers continuous vulnerability management, secure mobile deployment solutions, and expertise in separating signal from noise so you can focus on running your operation.
Workforce Design
BlackLake Security possesses the necessary technical proficiency and comprehension to effectively navigate through secure digital transformations. With an extensive pool of resources and a track record of successfully executed projects, we are committed to matching our areas of expertise to your objectives. Our aim is to bolster the capabilities of your internal teams, creating a partnership towards success.